Making Your WordPress Password Hashing Stronger with bcrypt
Development
WordPress uses the phpass framework and eight passes of MD5 hashing to encrypt registered user passwords. But you can make password encryption even stronger by upgrading from MD5 to bcrypt.

The WordPress core is secure but you can make the passwords stored in your site’s database even more secure by upgrading from MD5-based password hashing to bcrypt.
While some may say otherwise, the WordPress core really is secure, and it’s not that hard to keep your WordPress website safe from most common attacks by using a unique admin username and a strong password, keeping the core software up-to-date, using plugins and themes from reputable authors and keeping them updated, and using a good security plugin.
Implementing just a few additional security measures will ensure your site’s security will trend towards the far upper end of the security bell curve. However, if your website requires user login, there is one additional website security issue you need to think about: password encryption.
How to Start a Twitter Firestorm…
On March 1, 2016, WordPress development agency Roots announced the release of the WP Password bcrypt plugin. The post announcing the release of the plugin was covered by WP Tavern and was very critical of the WordPress core development team tasked with managing the password hashing function. The result was a small-scale Twitter firestorm between the post’s author and members of the WordPress core development team.
@swalkinshaw @retlehs @tw2113 @themeSurgeon @helenhousandi so yes, your post from March 1 is unfortunately alarmist and wrong.
— Andrew Nacin (@nacin) March 19, 2016
The gist of the matter was that some members of the WordPress community, such as Roots, believed MD5 hashing should be dropped immediately in favor of bcrypt, and that failing to do so demonstrated a lack of commitment to password security. However, the team that manages the wp_hash_password function maintained that the function produced results that were secure as-is.
How Does WordPress Password Hashing Work?
All of this back-and-forth begs the question: how does WordPress encrypt passwords?
The core WordPress wp_hash_password function uses the phpass password hashing framework and eight passes of MD5-based hashing. While MD5 hashing considered on its own is basically useless, WordPress’ password hashing function is not plain-vanilla MD5 hashing. The wp_hash_password function uses the phpass framework to combine key stretching with eight passes of MD5 to produce a hashing algorithm that is really quite good. However, that doesn’t mean it can’t and shouldn’t be improved.
When phpass is used, one of three hashing methods may be implemented: bcrypt, DES, and MD5. The recommendation made by the phpass developer is to go with bcrypt since it is the strongest of the three and to fallback to DES or MD5-based hashing only if bcrypt isn’t supported. However, by implementing MD5-based hashing, WordPress is able to maintain compatibility with legacy hosting platforms.
Phpass provides solid password encryption regardless of the hashing method implemented. However, when bcrypt is implemented, it takes much longer to calculate a hash than when other methods are implemented. The choice of hashing method doesn’t affect website users’ experience, and if someone attempts to brute-force their way through a database of hashed passwords it will take a lot longer to decipher the passwords if bcrypt hashing was used than if MD5 hashing was used.
In the end, the Roots team conceded that WordPress password hashing was stronger than their original post suggested, but maintained that hashing with bcrypt was significantly more secure than the hashing function implemented by the WordPress core team – a claim that is supported by my research into the matter.
Why Password Hashing Matters
Almost all security recommendations you hear about WordPress have to do with hardening a WordPress installation to make it harder to infiltrate. However, a very different type of threat also exists, especially for WordPress websites hosted on shared servers. What if the server itself is compromised and your WordPress database is copied? Your WordPress installation may be rock-solid, but if your host’s security measures are circumvented, your database could be copied without your website ever being hacked.
If that ever happens, all of the plain text data in your database would be easily read by whoever got around your host’s security measures. Only data that isn’t stored in plain text, such as your users’ passwords, would still be protected. The security of those encrypted passwords would then depend on the strength of the hashing method used the encrypt the passwords.
While the standard hashing method built into WordPress is pretty good, bcrypt is better.
It may seem trivial to worry about password hashing when your database has been compromised. Obviously, if that ever happens, the hashing method may be the last thing on your mind. However, keeping user passwords secure even once they’re in a hackers hands is critically important.
More than half of all internet users reuse the same password for most or all of their accounts. So if someone gets ahold of your website database and can decipher the passwords they will have at least two pieces of important information: user email addresses and the passwords those users used to create their accounts on your website. Armed with those two pieces of information, they will be able to gain access to the social media accounts, email accounts, and other online accounts of any users who made the mistake of reusing the same password over and over again.
Using bcrypt Password Hashing
It’s actually quite easy to switch from the standard hashing function to bcrypt. The WordPress hashing function is pluggable, meaning plugins can take over the password hashing function. In addition to the plugin developed and announced by Roots, there are also two plugins already in the official WordPress Plugin Directory that substitute bcrypt hashing for the standard hashing method.

Wp-bcrypt was created by independent plugin developer harrym, a.k.a. Harry Metcalfe, Managing Director of dxw works, a London-based WordPress and Ruby on Rails web development agency.
You’ll need to be running PHP 5.3+ to run this plugin. To install it, either download the plugin folder from WordPress.org and install it manually, or search for it from Plugins > Add New within the WordPress admin area.

Another option from the WordPress Plugin Directory is WP Hash Password. This plugin was created by an independent plugin developer from Germany named Ninos Ego. You can either download the plugin file from WordPress.org and install it manually, or search for it from Plugins > Add New within the WordPress admin area. The same PHP version limitation that applies to the WP bcrypt plugin also applies to this plugin. So you’ll need to be running PHP 5.3 or higher to use it.

The bcrypt plugin from Roots is a bit different from the plugins available from the WordPress Plugin Directory. Both of the plugins in the WordPress Plugin Directory use the same phpass framework as the WordPress core but upgrade from MD5-based to bcrypt hashing. Roots’ plugin doesn’t rely on phpass. Instead, it uses the password_hash and password_verify functions built into PHP 5.5+. As a result, you need to be running PHP 5.5 or higher to use this plugin.
The plugin is available as a Composer library. If you already use Composer, loading the plugin with Composer is the easiest way to get up and running. If you don’t use Composer to manage your WordPress installation (and the vast majority of our readers probably don’t), you can install the plugin manually.
Step 1: Make Sure You Have a Must-Use Plugins Folder
The developer recommends installing the plugin in the mu-plugins directory so that users can’t deactivate it. If you’ve never worked with must-use plugins before, you’ll need to create the directory. Just use an FTP client to access the wp-content directory and create a new directory named mu-plugins. If you want more detailed instructions, our WordPress manual has you covered.
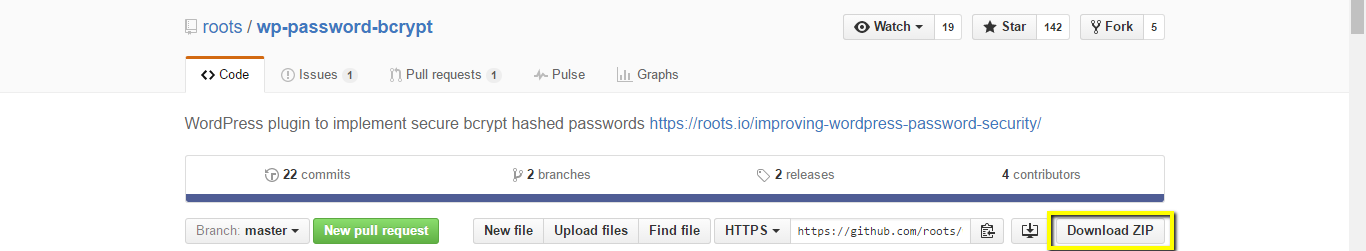
Step 2: Download the Plugin File from GitHub
The plugin isn’t available from the WordPress Plugin Directory. Instead, it is hosted at GitHub and available for free download. Head to the plugin page on GitHub and click Download ZIP. The plugin will be downloaded as a zip-format file to your computer.
Step 3: Install the Plugin
First, find the downloaded plugin zip folder on your computer. Next, extract the file locally on your computer. Then use an FTP client to copy the file named wp-password-bcrypt.php into the mu-plugins directory on the web server.
Note: Unlike most manually-installed plugins, you don’t want to copy the entire plugin folder to the server. Make sure you only copy the file named wp-password-bcrypt.php, and make sure to copy it directly into the mu-plugins directory.

The plugin will be activated automatically. If you visit Plugins > Installed Plugins and click on Must-Use you will see the WP Password bcrypt plugin is now activated.

Controversy Can be Good
The skirmish between the Roots and WordPress core developers shined a spotlight on the issue of password hashing. Now that the dust has settled we know two things:
- The hashing function included in the WordPress core is really pretty good.
- Upgrading to bcrypt hashing is easy and makes password hashing within WordPress even better.
What do you think? Is it worth upgrading to bcrypt password hashing or are you going to stick with the standard wp_hash_password function? Let us know what you think in the comments below.

Create your free account to post your comment
Login to post your comment